File Details |
|
| File Size | 1,855.5 MB |
|---|---|
| License | Shareware, $35.00 |
| Operating System | Windows (All) |
| Date Added | January 6, 2021 |
| Total Downloads | 9,206 |
| Publisher | SmartLine Inc. |
| Homepage | DeviceLock |
Publisher's Description
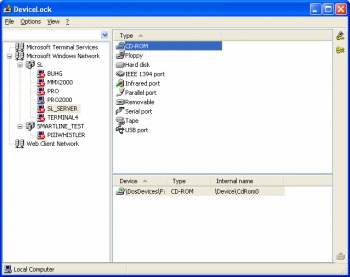
DeviceLock allows network administrators to specify which users can access which devices (ports, floppies, MOs, etc.) on the local computer. Once DeviceLock is installed, administrators can assign permissions to LPT ports, CD-ROMs, COM Ports, or any other device, just as they would to any share on the hard disk. Network administrators may use DeviceLock to flush a storage device's buffers and to get extended information about devices and NTFS partitions.
Latest Reviews
mikebray reviewed v8.0.54586 Beta 1 on Mar 12, 2014
awesome
jacobjackson reviewed v7.2.51171 on Aug 24, 2013
love this app
trynow reviewed v6.3 RC1 on Apr 7, 2008
WHY DONT THEY GIVE ABILITY TO INTERNET SECURITIES LOCKING DEVICES OF PC S. EVERY ATTACK COMES FROM WHO ARE INTERNET USERS OR NETWORK USERS. MOST USERS DO JOKE ATTACKS OR TRY TO SEE YOUR IMPORTANT FILES BY THE HELP OF YOUR OPERATING SYSTEMS CAPABILITY. IF YOU HAVE INTELLIGENT ON YOUR SYSTEM AND HARDWARE YOU
CAN LOCK THEM BUT SECURITY PROGRAMS MUST HAVE THIS ABILITY TOO.
raglionby reviewed v6.0 Beta 1 on Feb 4, 2006
We used DeviceLock initially, but as we added more systems to our network found it to be unreliable and ended up ditching it. We ended up switching to a product called DeviceWall, which was much easier to setup and also had security audit tools that the other products we reviewed did not.
yizuman reviewed v6.0 Beta 1 on Jan 6, 2006
ModderXManiac wrote: "Should be free"
Yes, shareware is evil! How dare they want to make money to feed their families and pay their bills!
We should hang all shareware authors for wanting money!
Let their kids starve because mommy or daddy isn't allowed to be successful and prosper so they can have food on their table!
/sarcasm off
Anybody else have a problem with shareware????
Pipewrench reviewed v5.7 Beta on Dec 6, 2004
Seems OK, but not that great. Fortress is better but Fortress is easily hacked.
Why would network admins need this? If you're a network admin you should be using Active Directory and and network permissions. If you need to lock devices out on a client PC you can do it with a Group Policy Object (GPO).
This software seems like it would only be good if you are in need to lock down your PC at home or in a dorm environment for students. Maybe if you don't want your roommate to have access to stuff.
-Pipewrench
MCSE, Linux+
Network Analyst
JCogzAtIntel reviewed v4.1.02 on Feb 25, 2000
Are you ready for some Network Power!!!!!
Great for administrators but not for home users. I reccomend advanced users to try this program. By disabling hardware devices on your computer, there is a risk of memory address crashes on local pc's. Not too bad for a network. I like fortres that offers a good security package.
Blue Dolphin reviewed v1.2 on Dec 15, 1999
Hi, I don't think this soft is useful and above all cunning !! Because When You have the DeviceLock's sharware, you can do the same thing, and for all the device !! Not just the simple CD...
mikebray reviewed v8.0.54586 Beta 1 on Mar 12, 2014
awesome
jacobjackson reviewed v7.2.51171 on Aug 24, 2013
love this app
trynow reviewed v6.3 RC1 on Apr 7, 2008
WHY DONT THEY GIVE ABILITY TO INTERNET SECURITIES LOCKING DEVICES OF PC S. EVERY ATTACK COMES FROM WHO ARE INTERNET USERS OR NETWORK USERS. MOST USERS DO JOKE ATTACKS OR TRY TO SEE YOUR IMPORTANT FILES BY THE HELP OF YOUR OPERATING SYSTEMS CAPABILITY. IF YOU HAVE INTELLIGENT ON YOUR SYSTEM AND HARDWARE YOU
CAN LOCK THEM BUT SECURITY PROGRAMS MUST HAVE THIS ABILITY TOO.
raglionby reviewed v6.0 Beta 1 on Feb 4, 2006
We used DeviceLock initially, but as we added more systems to our network found it to be unreliable and ended up ditching it. We ended up switching to a product called DeviceWall, which was much easier to setup and also had security audit tools that the other products we reviewed did not.
yizuman reviewed v6.0 Beta 1 on Jan 6, 2006
ModderXManiac wrote: "Should be free"
Yes, shareware is evil! How dare they want to make money to feed their families and pay their bills!
We should hang all shareware authors for wanting money!
Let their kids starve because mommy or daddy isn't allowed to be successful and prosper so they can have food on their table!
/sarcasm off
Anybody else have a problem with shareware????
Pipewrench reviewed v5.7 Beta on Dec 6, 2004
Seems OK, but not that great. Fortress is better but Fortress is easily hacked.
Why would network admins need this? If you're a network admin you should be using Active Directory and and network permissions. If you need to lock devices out on a client PC you can do it with a Group Policy Object (GPO).
This software seems like it would only be good if you are in need to lock down your PC at home or in a dorm environment for students. Maybe if you don't want your roommate to have access to stuff.
-Pipewrench
MCSE, Linux+
Network Analyst
JCogzAtIntel reviewed v4.1.02 on Feb 25, 2000
Are you ready for some Network Power!!!!!
Great for administrators but not for home users. I reccomend advanced users to try this program. By disabling hardware devices on your computer, there is a risk of memory address crashes on local pc's. Not too bad for a network. I like fortres that offers a good security package.
Blue Dolphin reviewed v1.2 on Dec 15, 1999
Hi, I don't think this soft is useful and above all cunning !! Because When You have the DeviceLock's sharware, you can do the same thing, and for all the device !! Not just the simple CD...